Malware analysis Malicious activity
Por um escritor misterioso
Descrição

How to Do Malware Analysis?

Malware analysis file Malicious activity

Malware Analysis Benefits Incident Response

Patch Now: Exploit Activity Mounts for Dangerous Apache Struts 2 Bug
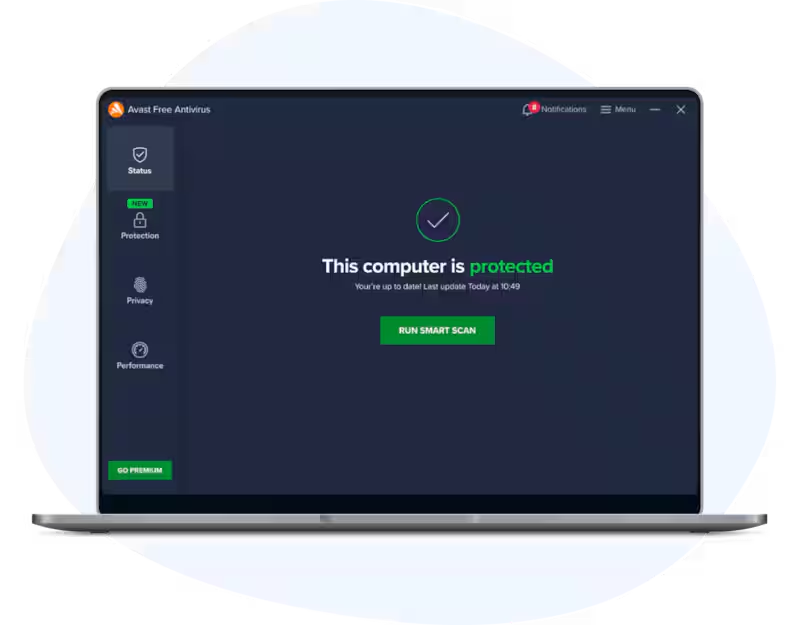
Download Free Antivirus Software
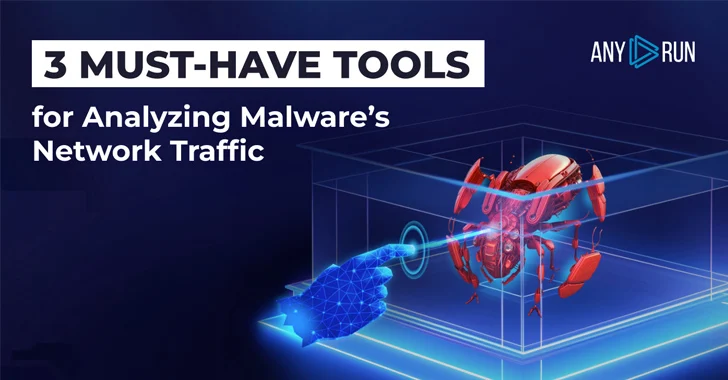
How to Analyze Malware's Network Traffic in A Sandbox

AlienVault - Open Threat Exchange

Malware analysis 1071d6d497a10cef44db396c07ccde65 Malicious activity

Malware Analysis Framework v1.0

Security Orchestration Use Case: Automating Malware Analysis - Palo Alto Networks Blog

Remediation and Malware Detection Overview

Cybersecurity Search Engine

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen

Malware Analysis: Steps & Examples - CrowdStrike

What is Malware? Definition, Types, Prevention - TechTarget
de
por adulto (o preço varia de acordo com o tamanho do grupo)