Malware analysis Malicious activity
Por um escritor misterioso
Descrição

Cybersecurity Search Engine

Unveiling activities of Tropic Trooper 2023 deep analysis of Xiangoop Loader and EntryShell payload

PROUD-MAL: static analysis-based progressive framework for deep unsupervised malware classification of windows portable executable

Mastering Malware Analysis

Malware analysis index.html Malicious activity

Endpoint Detection and Response, Free - What is EDR Security?

FBI, CISA, MS-ISAC release cybersecurity advisory on emerging Rhysida ransomware targeting critical sectors - Industrial Cyber
Download Free Antivirus Software

Malware analysis cd53fba6ddd4ae4ef7a5747c6003236c85791477854cc1b7ce00e0f8ee7677d9 Malicious activity

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen

What to Include in a Malware Analysis Report

Security Orchestration Use Case: Automating Malware Analysis - Palo Alto Networks Blog
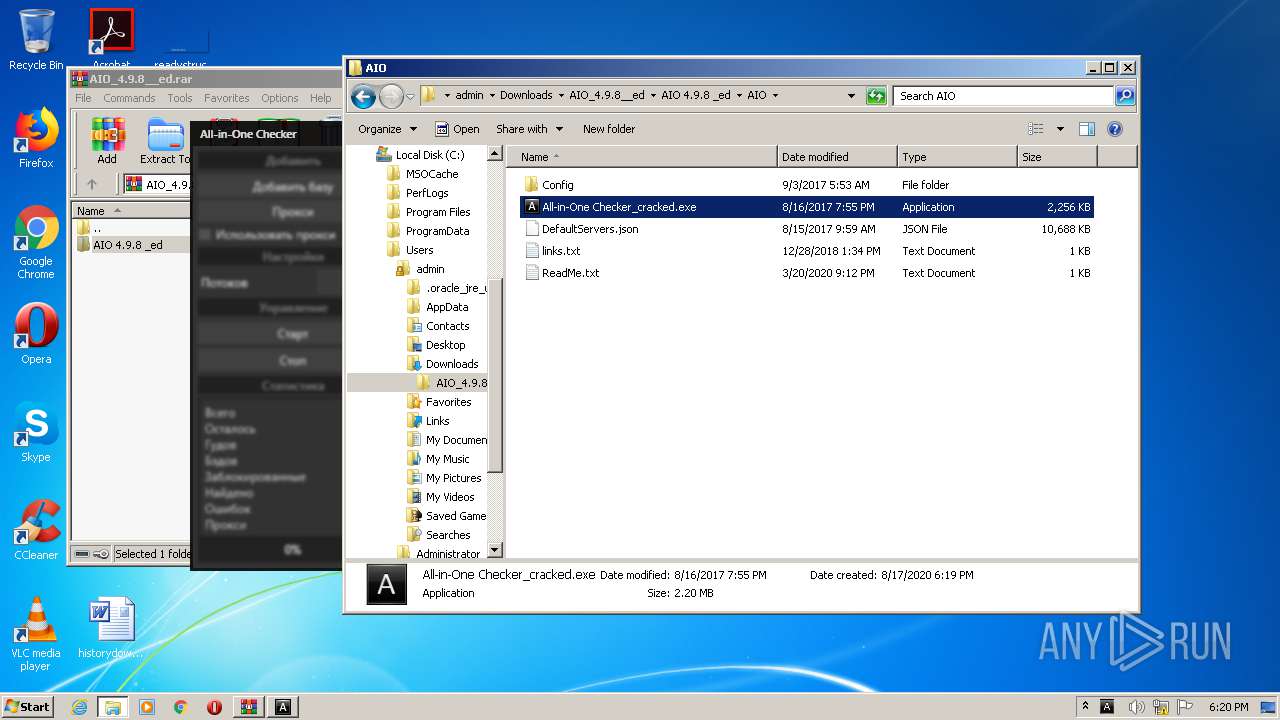
Malware analysis AIO_4.9.8__ed.rar Malicious activity

Patch Now: Exploit Activity Mounts for Dangerous Apache Struts 2 Bug
de
por adulto (o preço varia de acordo com o tamanho do grupo)