Trojan IT Security Matters
Por um escritor misterioso
Descrição
Posts about Trojan written by Klaus Jochem
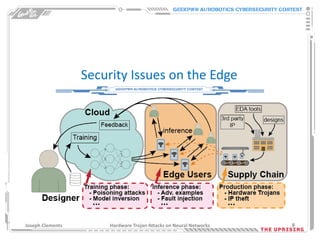
Hardware Trojan Attacks on Neural Networks - Joseph Clements - DEF

From pranks to APTs: How remote access Trojans became a major
In this short book, Dan Hill outlines a new vocabulary of design, one that needs to be smuggled into the upper echelons of power. He asserts that,

Dark Matter and Trojan Horses: A Strategic Design Vocabulary

Payment Security: 5 Ways To Remain Compliant

Trojan Horse - Plurilock

Software and Hardware level security in IoT

Remote access Trojans threaten network security - Allgeier secion

SVAMC-YP Tech Talks: Current Information Security Issues and

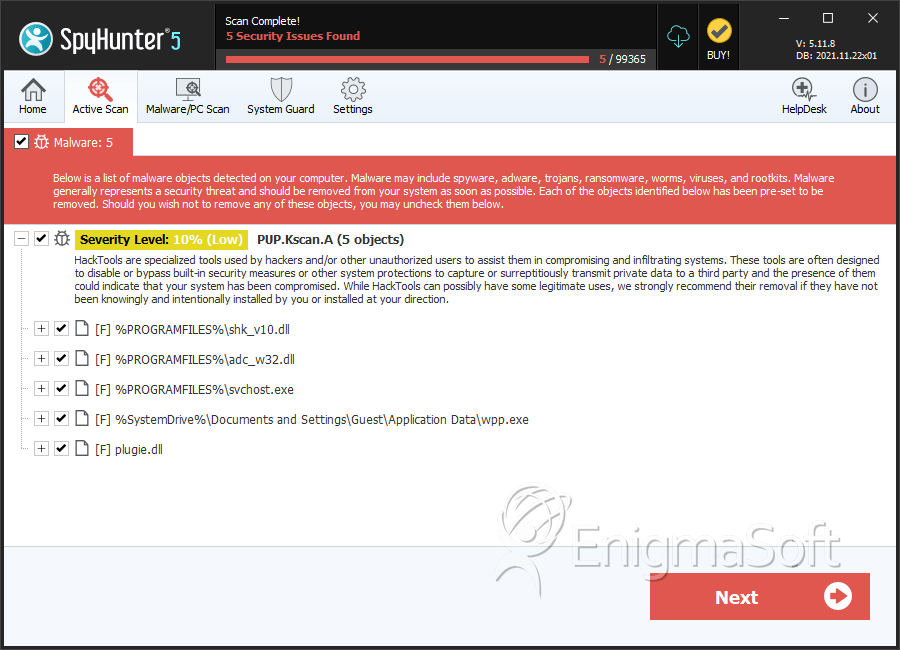
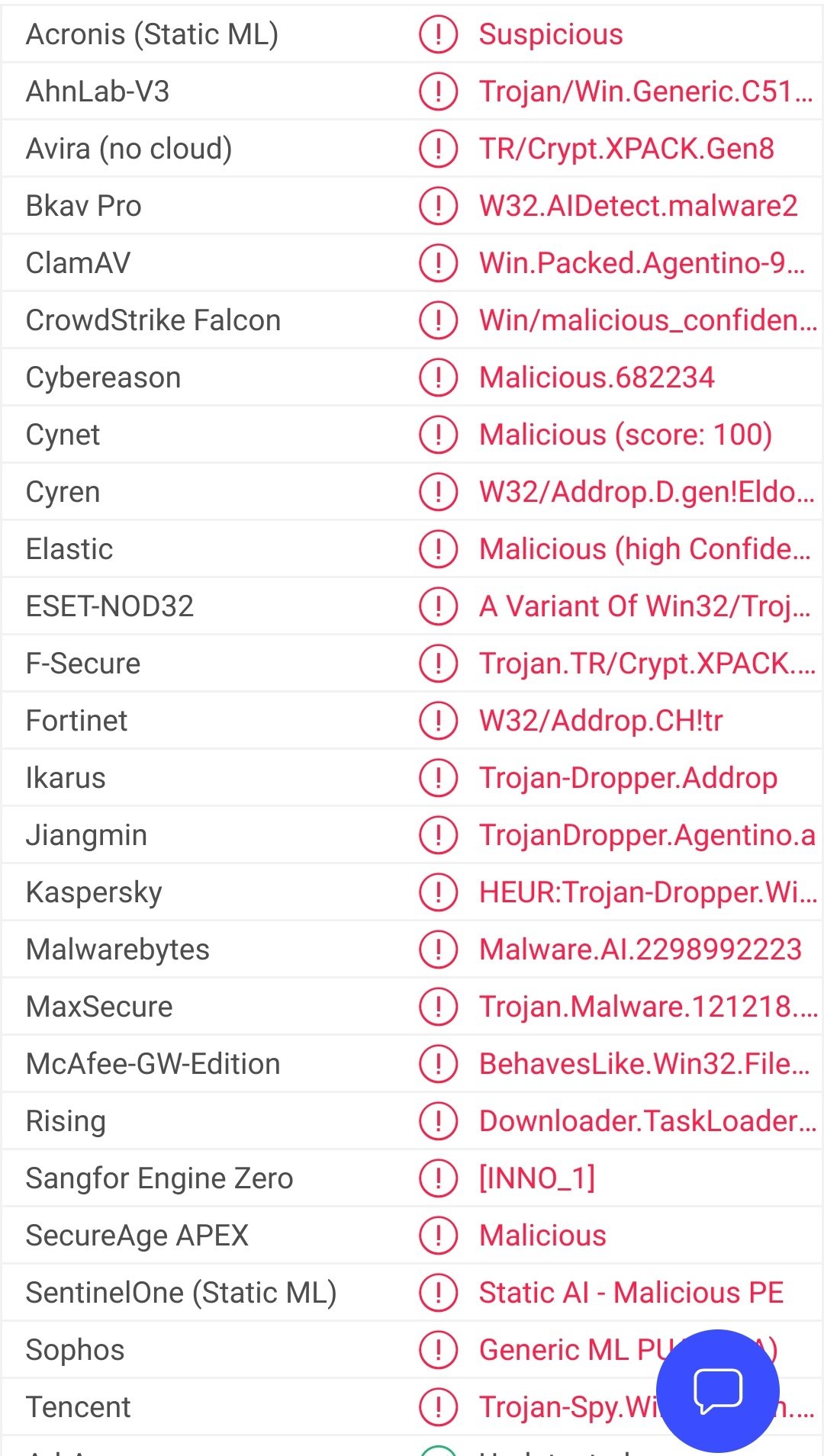
What Is a Trojan: a Virus or Malware? How Does It Work
Trojan Source' Bug Threatens the Security of All Code – Krebs on
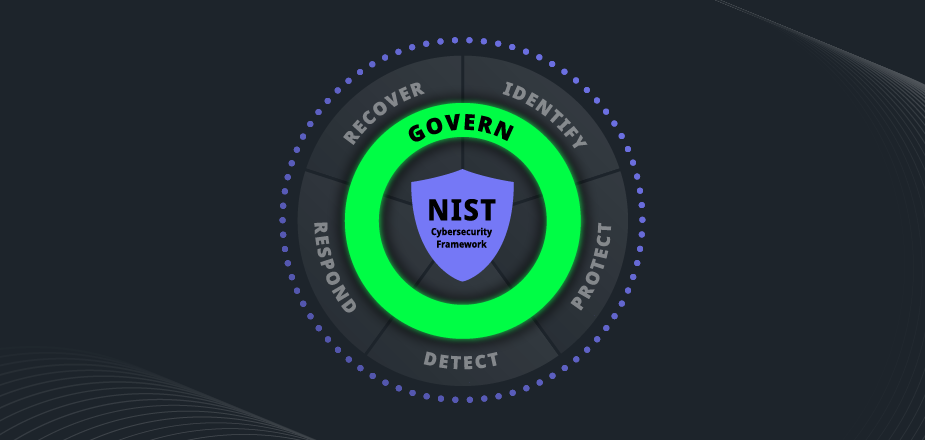
An insider's POV into NIST 2.0 updates
TWIM Ep154 Pt2: What Is & How To Stop/Remove Trojan:Win32/Casdet
The Kremlin's Trojan Horses 3.0 - Atlantic Council
de
por adulto (o preço varia de acordo com o tamanho do grupo)